What is a Firewall?
A firewall is a network security system that acts as a barrier between trusted internal networks and untrusted external networks (like the internet). It monitors and controls incoming and outgoing network traffic based on predetermined security rules, effectively serving as a gatekeeper for your network infrastructure.
How Firewalls Work
Firewalls operate by examining network packets and making decisions based on rules:
- Packet Inspection: Analyzes data packets for source/destination IP, port, protocol
- Rule Matching: Compares packet attributes against configured security rules
- Action Execution: Allows, blocks, or logs traffic based on matching rules
- State Tracking: Maintains connection state for more intelligent filtering
Types of Firewalls
Network-Based Firewalls
Packet-Filtering Firewalls
- Inspect packets at the network layer
- Make decisions based on IP addresses, ports, and protocols
- Fast but limited inspection depth
- Example rules:
ALLOW tcp from any to 203.0.113.45 port 443 BLOCK tcp from 198.51.100.0/24 to any port 22
Stateful Inspection Firewalls
- Track connection states (new, established, related)
- Understand protocol behaviors
- More secure than simple packet filtering
- Common in enterprise environments
Next-Generation Firewalls (NGFW)
- Deep packet inspection (DPI)
- Application-layer filtering
- Intrusion prevention systems (IPS)
- Malware detection and sandboxing
Application-Based Firewalls
Web Application Firewalls (WAF)
- Protect web applications from attacks
- Filter HTTP/HTTPS traffic
- Defend against:
- SQL injection
- Cross-site scripting (XSS)
- DDoS attacks
- OWASP Top 10 vulnerabilities
API Firewalls
- Specialized for API protection
- Validate request structures
- Enforce rate limiting
- Schema validation
Host-Based Firewalls
- Installed on individual devices
- Control traffic to/from that specific host
- Examples: Windows Firewall, iptables (Linux), pf (macOS)
Firewall Rules and Policies
Common Rule Components
interface FirewallRule {
action: 'allow' | 'deny' | 'reject';
protocol: 'tcp' | 'udp' | 'icmp' | 'any';
sourceIP: string;
sourcePort: number | string;
destinationIP: string;
destinationPort: number | string;
direction: 'inbound' | 'outbound';
}Best Practices
- Default Deny: Block everything except explicitly allowed traffic
- Principle of Least Privilege: Grant minimum necessary access
- Regular Audits: Review and update rules periodically
- Logging: Monitor blocked and allowed traffic for security analysis
Firewalls and Proxy Services
Common Firewall Challenges with APIs
When developing applications that consume external APIs, firewalls can cause issues:
Corporate Firewall Restrictions
// This might be blocked by corporate firewalls
fetch('https://api.external-service.com/data')
.catch(error => {
// Error: net::ERR_CONNECTION_REFUSED
// Firewall blocked outbound connection
});IP Whitelisting Requirements
Some APIs require your IP to be whitelisted:
Firewall Rule: ALLOW from 203.0.113.45 to api-server port 443
Problem: Dynamic IPs make whitelisting difficult
How CorsProxy Solves Firewall Issues
Centralized Egress Point
// Instead of many dynamic IPs hitting the API
const response = await fetch(
'https://corsproxy.io/?url=https://api.external-service.com/data',
{
headers: {
'x-cors-api-key': 'your-api-key'
}
}
);CorsProxy provides:
- Stable IP addresses for whitelisting
- Global edge network (330+ locations)
- Firewall-friendly request patterns
- Enterprise compliance for corporate environments
Bypassing Overly Restrictive Firewalls
// Corporate firewall blocks direct API access
// Route through CorsProxy instead
const corsProxyUrl = 'https://corsproxy.io/';
const targetUrl = 'https://blocked-api.com/endpoint';
const data = await fetch(corsProxyUrl + targetUrl, {
headers: {
'x-cors-api-key': process.env.CORS_API_KEY
}
}).then(r => r.json());Firewall Configuration for Web Services
Securing Your API Server
# Example iptables rules (Linux)
# Allow HTTPS from CorsProxy IPs
iptables -A INPUT -p tcp -s 104.26.0.0/20 --dport 443 -j ACCEPT
# Allow established connections
iptables -A INPUT -m state --state ESTABLISHED,RELATED -j ACCEPT
# Block all other inbound traffic
iptables -A INPUT -j DROPCloudflare WAF Integration
CorsProxy leverages Cloudflare’s Web Application Firewall:
- DDoS protection at the edge
- Rate limiting per API key
- Threat intelligence feeds
- Custom security rules
Common Firewall Attacks and Defenses
Firewall Evasion Techniques
Attackers may attempt to bypass firewalls using:
- Port scanning: Finding open ports
- Protocol tunneling: Hiding traffic in allowed protocols
- Fragmentation attacks: Splitting packets to evade inspection
- Application-layer exploits: Attacking allowed services
CorsProxy Security Measures
- TLS/SSL encryption for all traffic
- Request validation and sanitization
- Automated threat detection
- Rate limiting and abuse prevention
- IP reputation filtering
Firewall Logs and Monitoring
What to Log
- Denied connection attempts
- Allowed traffic patterns
- Anomalous behavior
- Failed authentication attempts
Example Log Entry
2024-01-15 14:32:10 DENY TCP 198.51.100.45:54321 -> 203.0.113.45:22
Reason: Unauthorized SSH attempt
Action: Blocked and logged
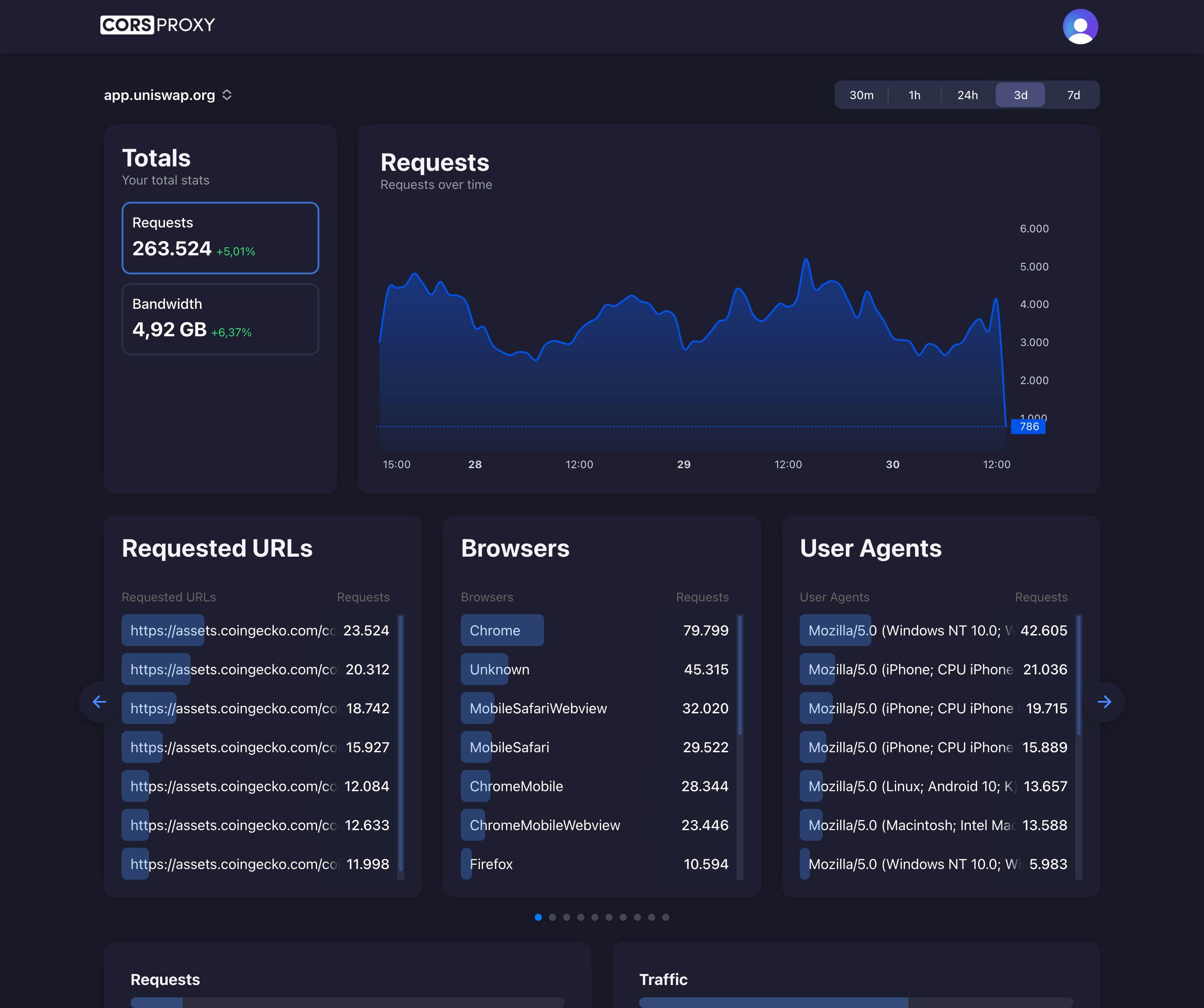
Monitoring with CorsProxy
CorsProxy provides dashboards for:
- Request volume by region
- Blocked requests and reasons
- Rate limit violations
- Error rates and types
Firewall Rules for Development
Local Development
# Allow localhost traffic
iptables -A INPUT -i lo -j ACCEPT
# Allow development ports
iptables -A INPUT -p tcp --dport 3000 -j ACCEPT # React dev server
iptables -A INPUT -p tcp --dport 8080 -j ACCEPT # API serverStaging Environment
// Restrict staging API to office IPs
const allowedIPs = [
'203.0.113.0/24', // Office network
'198.51.100.45' // VPN gateway
];
// CorsProxy can enforce IP restrictionsCompliance and Firewalls
Different regulations mandate firewall requirements:
PCI DSS (Payment Card Industry)
- Firewall between untrusted networks and cardholder data
- Deny all traffic except explicitly allowed
- Regular firewall rule reviews
HIPAA (Healthcare)
- Network segmentation via firewalls
- Audit logging of firewall changes
- Intrusion detection systems
SOC 2
- Documented firewall policies
- Change management processes
- Regular security assessments
CorsProxy maintains compliance with major security standards. See our security documentation for details.
Troubleshooting Firewall Issues
Common Problems
// Problem 1: Firewall blocking outbound requests
// Solution: Use CorsProxy as intermediary
// Problem 2: Rate limiting by firewall
// Solution: Distribute requests across CorsProxy's global network
// Problem 3: IP whitelisting required
// Solution: Whitelist CorsProxy's stable IP rangesDebugging Tips
- Check firewall logs for blocked connections
- Verify DNS resolution isn’t being filtered
- Test with curl to isolate issues
- Use traceroute to identify where packets are dropped
# Test connectivity through firewall
curl -v https://api.example.com/endpoint
# Test via CorsProxy
curl -v https://corsproxy.io/?url=https://api.example.com/endpoint \
-H "x-cors-api-key: your-key"Best Practices for Production
- Layer Security: Use firewalls alongside other security measures
- Regular Updates: Keep firewall rules current with business needs
- Monitoring: Set up alerts for suspicious patterns
- Documentation: Maintain clear records of firewall rules and purposes
- Testing: Verify rules don’t block legitimate traffic