If you’re a developer with Indian users, you’ve probably noticed something alarming: your Supabase app suddenly stopped working in India. No error message. No warning. Just silence — your API calls time out, authentication fails, and your users see a blank screen or broken app.
You’re not alone. Thousands of developers building on Supabase are dealing with the same problem right now. The issue isn’t your code, your Supabase configuration, or your hosting — it’s DNS-level blocking by Indian ISPs.
This guide explains exactly what happened, which ISPs are affected, and — most importantly — how to fix it so your app works again for every user in India. The fix takes one line of code.
Table of Contents
- What Happened — Why Supabase Is Blocked
- Which ISPs Are Affected
- How DNS Poisoning Works
- What Breaks When Supabase Is Blocked
- Fix 1: CORSPROXY — The One-Line Fix (Recommended)
- Fix 2: Configure the Supabase JS Client
- Fix 3: Proxy Individual Supabase Services
- What About VPNs and Custom DNS?
- Performance Impact
- Security Considerations
- FAQ
- Conclusion
What Happened — Why Supabase Is Blocked
In late 2024, the Indian Ministry of Electronics and Information Technology (MeitY) issued orders to ISPs to block access to certain domains, and *.supabase.co ended up on the list. The exact reasoning has not been made fully public, but the consequence is clear: every Supabase-powered application is broken for Indian internet users.
ISPs were instructed to implement the block at the DNS level. This means that when a user on Jio, Airtel, or ACT Fibernet tries to resolve your-project.supabase.co, their ISP’s DNS server returns either nothing or a wrong IP address. The connection simply times out.
This is not a temporary outage. The block has been in place for months and shows no sign of being lifted. If your app depends on Supabase, you need a workaround — and you need it now.
How developers discover the problem
Most developers discover this through user complaints:
- “Your app isn’t loading for me” (from Indian users)
- Users report blank screens, infinite loading spinners, or “network error” messages
- Your error monitoring shows a spike in
ERR_CONNECTION_TIMED_OUTerrors from Indian IPs - Everything works fine when you test from outside India
If you’re seeing these symptoms, the Supabase DNS block is almost certainly the cause.
Which ISPs Are Affected
The block is widespread across India’s largest ISPs. Here’s a breakdown:
| ISP | Subscribers | Block Method | Status |
|---|---|---|---|
| Jio (Fiber & Mobile) | 400M+ | DNS poisoning | Active |
| Airtel (Broadband & Mobile) | 350M+ | DNS poisoning | Active |
| ACT Fibernet | 2M+ | DNS poisoning | Active |
| BSNL | 100M+ | DNS poisoning | Reported in some regions |
| Vi (Vodafone Idea) | 200M+ | DNS poisoning | Reported in some regions |
Combined, these ISPs serve over 500 million internet users in India. That’s potentially half a billion people who cannot access your Supabase-powered app.
Jio is by far the largest, with over 400 million subscribers across both mobile and fiber broadband. If your app has any Indian users, there’s a very high chance they’re on Jio.
How DNS Poisoning Works
To understand why your app is broken — and why the fix works — you need to understand what DNS poisoning does.
Normal DNS resolution
When a browser needs to reach your-project.supabase.co, here’s what normally happens:
- Browser asks the ISP’s DNS server: “What’s the IP for
your-project.supabase.co?” - DNS server responds: “It’s
104.18.x.x” (Supabase’s actual server IP) - Browser connects to that IP and loads your data
DNS poisoning (what’s happening in India)
With DNS poisoning, the ISP tampers with step 2:
- Browser asks the ISP’s DNS server: “What’s the IP for
your-project.supabase.co?” - DNS server responds with nothing (NXDOMAIN) or a wrong IP (like
0.0.0.0or a government block page) - Browser cannot connect. The request times out or fails immediately.
The key point: the ISP never blocks the actual network traffic. They only tamper with DNS resolution. This means that if your app can reach Supabase through a different path — one that doesn’t rely on the ISP’s poisoned DNS — everything works.
That’s exactly what CORSPROXY does: it routes your Supabase requests through Cloudflare’s global network, which uses its own DNS resolution. The ISP’s poisoned DNS is never consulted.
Why changing DNS settings isn’t a real fix
You might think: “Just tell users to switch to Google DNS (8.8.8.8) or Cloudflare DNS (1.1.1.1).” There are two problems:
- Most ISPs intercept DNS traffic regardless of which DNS server you configure. Even if a user sets their DNS to 8.8.8.8, many Indian ISPs transparently redirect DNS queries to their own servers.
- You can’t ask your users to change system settings. The vast majority of your users don’t know what DNS is, and they shouldn’t have to. Your app should just work.
What Breaks When Supabase Is Blocked
When *.supabase.co is blocked, everything that talks to Supabase fails. Here’s what breaks:
REST API (PostgREST)
All database queries fail. Any call to /rest/v1/ times out:
// This times out in India
const { data } = await supabase.from('todos').select('*');
// Error: TypeError: Failed to fetchAuthentication (GoTrue)
Login, signup, magic links, OAuth — all broken:
// This times out in India
const { data, error } = await supabase.auth.signInWithPassword({
email: 'user@example.com',
password: 'password'
});
// Error: AuthRetryableFetchErrorStorage
File uploads, downloads, and image transformations fail:
// This times out in India
const { data } = await supabase.storage.from('avatars').download('photo.png');
// Error: StorageApiErrorRealtime
WebSocket connections can’t establish:
// This never connects in India
const channel = supabase.channel('room1')
.on('broadcast', { event: 'message' }, (payload) => {
console.log(payload); // Never fires
})
.subscribe();Edge Functions
Custom serverless functions are unreachable:
// This times out in India
const { data } = await supabase.functions.invoke('process-payment');
// Error: FunctionsHttpErrorThe bottom line: if your app uses Supabase for anything, it’s completely broken for Indian users. Not partially broken — completely broken.
Fix 1: CORSPROXY — The One-Line Fix (Recommended)
The fastest way to unblock Supabase for Indian users is CORSPROXY. It routes your Supabase requests through Cloudflare’s global edge network, which has its own DNS resolution and is not affected by Indian ISP blocks.
Basic fetch example
If you’re making direct REST calls to Supabase:
// Before (blocked in India)
const response = await fetch(
'https://your-project.supabase.co/rest/v1/todos',
{
headers: {
'apikey': 'your-anon-key',
'Authorization': 'Bearer your-anon-key'
}
}
);
// After (works everywhere)
const PROXY = 'https://corsproxy.io/?url=';
const response = await fetch(
PROXY + encodeURIComponent('https://your-project.supabase.co/rest/v1/todos'),
{
headers: {
'apikey': 'your-anon-key',
'Authorization': 'Bearer your-anon-key'
}
}
);
const todos = await response.json();That’s it. One line changed. Your Supabase REST API now works for every user in India.
How it works under the hood
- Your app sends the request to
corsproxy.ioinstead ofsupabase.co - CORSPROXY receives the request at the nearest Cloudflare edge location (there are 330+ worldwide, including multiple in India)
- CORSPROXY resolves
your-project.supabase.cousing Cloudflare’s own DNS — bypassing the ISP’s poisoned DNS - CORSPROXY forwards the request to Supabase and returns the response to your app
- All headers, cookies, and authentication tokens are preserved
The entire proxy hop adds approximately 25ms of latency, which is imperceptible to users.
Fix 2: Configure the Supabase JS Client
If you’re using the official @supabase/supabase-js client library, you can configure it to route all requests through CORSPROXY with a custom fetch function:
import { createClient } from '@supabase/supabase-js';
const PROXY = 'https://corsproxy.io/?url=';
const SUPABASE_URL = 'https://your-project.supabase.co';
const SUPABASE_ANON_KEY = 'your-anon-key';
const supabase = createClient(SUPABASE_URL, SUPABASE_ANON_KEY, {
global: {
fetch: (url, options = {}) => {
// Route all Supabase requests through CORSPROXY
const proxiedUrl = PROXY + encodeURIComponent(url.toString());
return fetch(proxiedUrl, options);
}
}
});Now every Supabase operation automatically goes through the proxy:
// All of these now work in India — no other changes needed
// Database queries
const { data: todos } = await supabase.from('todos').select('*');
// Authentication
const { data: auth } = await supabase.auth.signInWithPassword({
email: 'user@example.com',
password: 'password'
});
// Storage
const { data: file } = await supabase.storage
.from('avatars')
.download('photo.png');
// Edge Functions
const { data: result } = await supabase.functions.invoke('hello');This is the recommended approach if you’re using the Supabase JS client. You change one configuration, and every API call in your entire app is automatically unblocked.
Conditional proxying (only for Indian users)
If you only want to proxy for users who are actually affected by the block, you can detect the user’s location and conditionally enable the proxy:
const isIndia = Intl.DateTimeZone
? Intl.DateTimeFormat().resolvedOptions().timeZone === 'Asia/Kolkata'
: false;
const supabase = createClient(SUPABASE_URL, SUPABASE_ANON_KEY, {
global: {
fetch: isIndia
? (url, options = {}) => {
const proxiedUrl = PROXY + encodeURIComponent(url.toString());
return fetch(proxiedUrl, options);
}
: undefined
}
});However, we recommend proxying all traffic rather than conditionally. The latency overhead is minimal (25ms), and you don’t risk misdetecting a user’s location. It also protects against future blocks in other regions.
Fix 3: Proxy Individual Supabase Services
If you prefer more granular control, you can proxy individual Supabase services separately:
REST API
const PROXY = 'https://corsproxy.io/?url=';
const BASE = 'https://your-project.supabase.co';
// Query your database
const response = await fetch(
PROXY + encodeURIComponent(`${BASE}/rest/v1/todos?select=*`),
{
headers: {
'apikey': 'your-anon-key',
'Authorization': 'Bearer your-anon-key',
'Content-Type': 'application/json'
}
}
);Authentication
// Sign up
const signupResponse = await fetch(
PROXY + encodeURIComponent(`${BASE}/auth/v1/signup`),
{
method: 'POST',
headers: {
'apikey': 'your-anon-key',
'Content-Type': 'application/json'
},
body: JSON.stringify({
email: 'user@example.com',
password: 'secure-password'
})
}
);
// Sign in
const signinResponse = await fetch(
PROXY + encodeURIComponent(`${BASE}/auth/v1/token?grant_type=password`),
{
method: 'POST',
headers: {
'apikey': 'your-anon-key',
'Content-Type': 'application/json'
},
body: JSON.stringify({
email: 'user@example.com',
password: 'secure-password'
})
}
);Storage
// Upload a file
const formData = new FormData();
formData.append('file', fileBlob);
const uploadResponse = await fetch(
PROXY + encodeURIComponent(`${BASE}/storage/v1/object/avatars/photo.png`),
{
method: 'POST',
headers: {
'apikey': 'your-anon-key',
'Authorization': 'Bearer user-jwt-token'
},
body: formData
}
);
// Download a file
const downloadResponse = await fetch(
PROXY + encodeURIComponent(`${BASE}/storage/v1/object/public/avatars/photo.png`)
);Edge Functions
const fnResponse = await fetch(
PROXY + encodeURIComponent(`${BASE}/functions/v1/process-payment`),
{
method: 'POST',
headers: {
'apikey': 'your-anon-key',
'Authorization': 'Bearer user-jwt-token',
'Content-Type': 'application/json'
},
body: JSON.stringify({ amount: 1000, currency: 'INR' })
}
);What About VPNs and Custom DNS?
When the block first hit, many developers and users turned to VPNs and custom DNS settings. Here’s why these don’t work as long-term solutions:
VPNs
The problem: You can’t ask your end users to install and run a VPN just to use your app. A VPN is a solution for developers testing their own apps — not a solution for your users.
- Most users don’t know what a VPN is
- Free VPNs are slow and unreliable
- Paid VPNs add monthly costs for your users
- VPNs add significant latency (100-300ms typically)
- Some Indian ISPs actively block VPN protocols too
Custom DNS (8.8.8.8, 1.1.1.1)
The problem: Many Indian ISPs intercept DNS traffic using transparent DNS proxying. Even if a user configures Google DNS or Cloudflare DNS on their device, the ISP can redirect those queries to their own poisoned DNS servers.
- DNS-over-HTTPS (DoH) can bypass this, but requires browser configuration most users can’t do
- Router-level DNS changes don’t help if the ISP intercepts at the network level
- Mobile users on Jio/Airtel often can’t change DNS settings at all
JioBase and similar tools
JioBase is a community project that was created specifically to help with this problem. It’s a valid approach, but CORSPROXY offers several advantages:
- 330+ edge locations worldwide vs. a single-region proxy
- 99.9% uptime SLA with enterprise-grade infrastructure
- Free tier with generous limits for development and small apps
- Cloudflare network backbone — the same infrastructure used by 20% of the internet
Performance Impact
A common concern: “Won’t routing through a proxy add latency?”
The short answer: yes, but it’s negligible.
Latency benchmarks
| Route | Latency |
|---|---|
| Direct to Supabase (from outside India) | ~40-80ms |
| Through CORSPROXY (from India) | ~65-105ms |
| Added by proxy | ~25ms |
CORSPROXY adds approximately 25ms of latency. For context:
- A human blink takes 100-400ms
- A typical user considers anything under 200ms to be “instant”
- The DNS block adds infinite latency (the request never completes)
So you’re trading “broken” for “25ms slower” — not much of a trade-off.
Why latency is so low
CORSPROXY runs on Cloudflare’s global edge network with 330+ data centers worldwide, including multiple locations in India (Mumbai, Chennai, New Delhi, Kolkata, and more). When an Indian user makes a request:
- The request hits the nearest Cloudflare edge (often in the same city)
- CORSPROXY resolves Supabase’s DNS using Cloudflare’s internal DNS (microseconds)
- The request is forwarded to Supabase (which also uses Cloudflare in many regions)
Because both CORSPROXY and Supabase run on or near Cloudflare’s network, the proxy hop is extremely fast.
Security Considerations
Security is a common concern when routing traffic through a third-party proxy. Here’s what you need to know:
Row-Level Security (RLS) still works
Supabase’s Row-Level Security policies are enforced on the Supabase server, not in the client. Since CORSPROXY forwards your requests to Supabase unchanged (including all headers and authentication tokens), RLS policies work exactly as configured.
HTTPS end-to-end
CORSPROXY uses HTTPS for both legs of the connection:
- Your app → CORSPROXY: HTTPS (TLS encrypted)
- CORSPROXY → Supabase: HTTPS (TLS encrypted)
Your data is encrypted in transit throughout the entire journey.
API keys and anon keys
Your Supabase anon key is designed to be public — it’s included in client-side code by design. Supabase’s security model relies on RLS policies, not key secrecy. Routing through CORSPROXY doesn’t change this security model.
If you’re using a service_role key (which should never be in client-side code), don’t route it through any client-side proxy. Service role keys should only be used in server-side code.
What CORSPROXY can see
CORSPROXY processes requests in transit, which means it can technically see:
- The URL you’re requesting
- Request headers (including auth tokens)
- Request and response bodies
This is the same trust model as any CDN or reverse proxy (including Cloudflare itself, which Supabase uses). CORSPROXY does not log request bodies or authentication tokens. See our privacy policy for details.
For applications handling highly sensitive data (healthcare, financial), consider using CORSPROXY’s dedicated proxy option, which provides an isolated instance.
FAQ
Will this fix work if the block gets lifted?
Yes. CORSPROXY works whether or not the block is active. If the block is lifted, your proxied requests will still work — they’ll just have slightly lower latency since the DNS resolution path is shorter.
Does this work with Supabase Realtime (WebSockets)?
CORSPROXY’s HTTP proxy works with REST API, Auth, Storage, and Edge Functions. For Realtime WebSocket connections, you may need to use CORSPROXY’s WebSocket support or configure your Realtime client to connect through the proxy. The HTTP-based Supabase operations (which are the majority of API calls) work out of the box.
Can I use this in production?
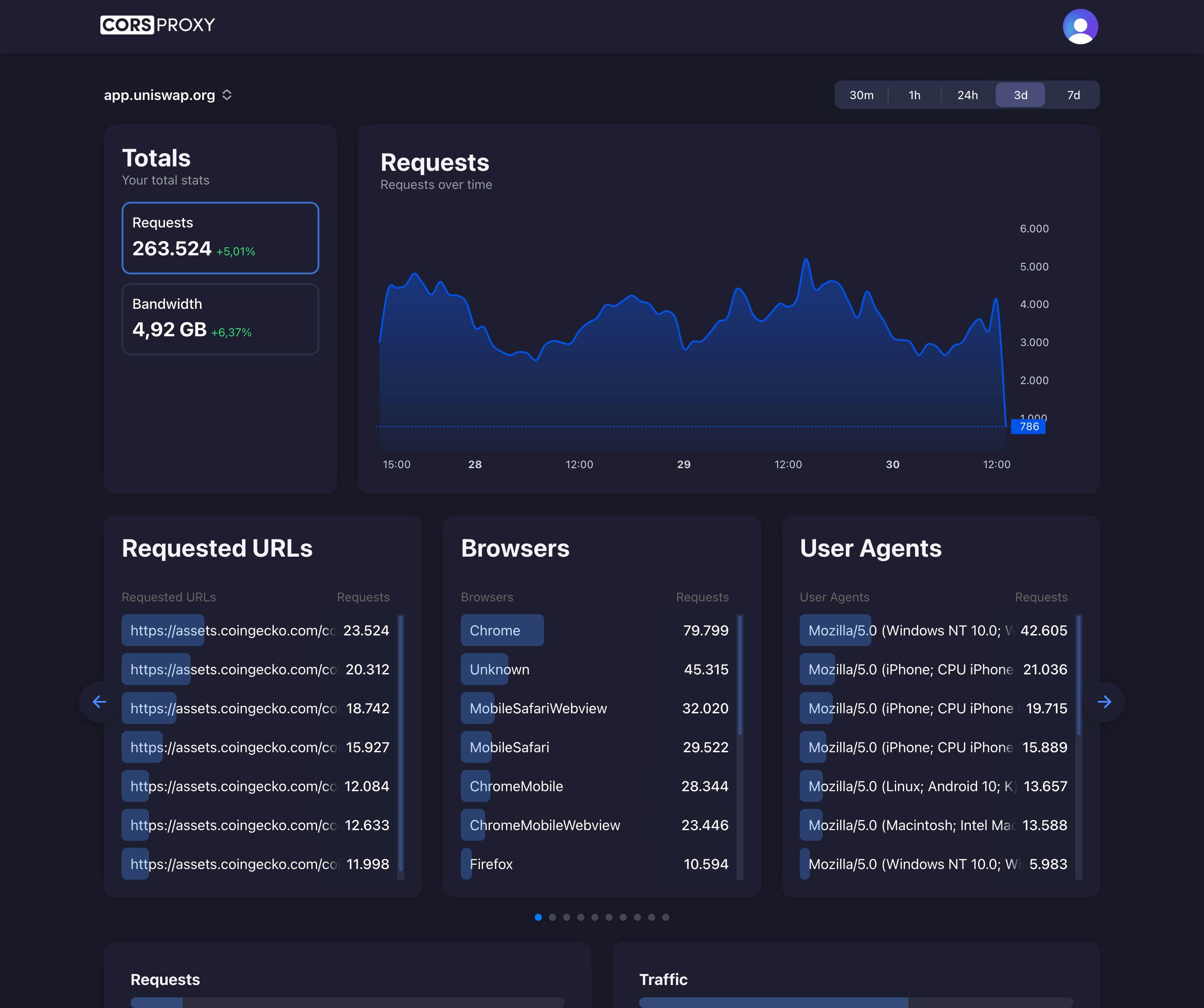
Yes. CORSPROXY is used in production by thousands of applications, including Uniswap (4M+ requests/month). For production use, we recommend a paid plan for higher rate limits, dedicated support, and SLA guarantees.
Does this work with Supabase’s self-hosted version?
If you’re self-hosting Supabase on a domain that’s not blocked, you don’t need a proxy. If your self-hosted domain is also blocked, yes, CORSPROXY works with any domain.
How is this different from a reverse proxy I set up myself?
CORSPROXY gives you the same functionality as a self-hosted reverse proxy, but without the operational overhead:
- No server to provision, secure, or maintain
- No SSL certificates to manage
- No scaling to worry about
- 330+ edge locations vs. a single server
- Free tier for development and small apps
Will Supabase eventually fix this?
Supabase has acknowledged the issue but cannot control ISP-level DNS blocking. Some developers have suggested Supabase offer custom domains or alternative endpoints, but as of early 2026, no official solution has been announced. Using a proxy like CORSPROXY is the recommended workaround.
Conclusion
The Supabase DNS block in India is frustrating, but the fix is straightforward:
- Fastest fix: Prefix your Supabase URLs with
https://corsproxy.io/?url= - Best for JS client users: Configure a custom
fetchfunction increateClient - For granular control: Proxy individual Supabase services (REST, Auth, Storage, etc.)
All three approaches take minutes to implement and immediately restore your app for hundreds of millions of Indian users.
Don’t wait for the block to be lifted — it may never be. Fix it now.
Ready to unblock your Supabase app?
- Get started free on CORSPROXY Console
- Read the full Supabase solution page
- Fix Supabase CORS errors (related guide for CORS-specific issues)
- View pricing for production apps