What is a Forward Proxy?
A forward proxy (or simply “proxy”) sits between client devices and the internet, forwarding requests from clients to external servers. Forward proxies serve clients by hiding their identity, controlling access to external resources, caching content, and providing additional security and privacy features.
Forward proxies represent the traditional proxy model most users encounter—corporate networks use forward proxies to control employee internet access, individuals use them for privacy and bypassing geo-restrictions, and developers use them for testing and scraping operations. The proxy acts on behalf of the client, making requests to the internet as if the proxy itself were the original requester.
How Forward Proxies Work
When a client configures a forward proxy, all outbound internet requests route through the proxy server instead of going directly to destination websites. The client sends requests to the proxy including the target URL, the proxy examines and potentially modifies the request, forwards it to the destination server, receives the response, and returns it to the client.
This intermediary position enables forward proxies to implement access controls blocking specific websites or categories, cache frequently accessed content reducing bandwidth and improving performance, hide client IP addresses providing privacy and anonymity, and scan traffic for malware or policy violations before allowing access.
Forward Proxy vs Reverse Proxy
Forward and reverse proxies serve opposite sides of network communications. Forward proxies sit client-side between users and the internet, serving client needs like privacy, access control, and caching. Clients explicitly configure forward proxy settings in browsers or applications.
Reverse proxies sit server-side between the internet and backend servers, serving server needs like load balancing, SSL termination, and security. Clients remain unaware of reverse proxies—they simply connect to what appears to be the destination server while the reverse proxy handles backend complexity transparently.
Forward proxies hide client identities from destination servers. Reverse proxies hide server infrastructure from clients. Both provide caching and security benefits but for different parties and purposes.
Forward Proxy Use Cases
Corporate Internet Access Control
Organizations deploy forward proxies to control and monitor employee internet usage. Proxy policies block access to inappropriate or unproductive websites, scan downloads for malware, enforce acceptable use policies, and log all internet activity for security auditing and compliance.
Forward proxies enable granular control—allowing business-related sites while blocking social media during work hours, limiting bandwidth-intensive streaming services, and requiring authentication for internet access. This centralized control point simplifies network security and policy enforcement across the entire organization.
Privacy and Anonymity
Individuals use forward proxies to hide their real IP addresses and locations from websites they visit. The destination server sees requests coming from the proxy IP rather than the user’s actual IP, preventing tracking, avoiding targeted advertising, and accessing content without revealing personal information.
Privacy-focused forward proxies filter identifying headers, block tracking cookies, and normalize request patterns making users less identifiable across sessions and websites. This anonymization protects against surveillance, profiling, and location-based restrictions.
Web Scraping Operations
Web scraping requires forward proxies to avoid detection and IP bans. Making thousands of requests from a single IP triggers rate limiting and blocking. Forward proxies distribute scraping traffic across multiple IP addresses, maintaining reasonable request rates per IP while achieving high total throughput.
Rotating forward proxies automatically change IP addresses between requests or at time intervals, making scraping operations appear as normal traffic from many users rather than automated activity from a single source.
Geo-Restriction Bypass
Content providers implement geographic restrictions based on visitor IP addresses. Forward proxies located in permitted regions enable accessing geo-blocked content by making requests appear to originate from allowed locations.
Users connect to forward proxies in specific countries to access region-locked streaming services, regional websites, or localized content unavailable from their actual location. The proxy’s geographic location determines what content the user can access regardless of their true physical location.
Using Forward Proxies with CorsProxy
CorsProxy provides forward proxy capabilities through HTTP parameters, eliminating proxy configuration and infrastructure management:
// Access any resource through CorsProxy forward proxy
const response = await fetch(
`https://corsproxy.io/?url=${encodeURIComponent('https://api.example.com/data')}&key=your-api-key&type=residential&colo=fra`
);
const data = await response.json();
// All forward proxy benefits without configurationThis approach provides forward proxy advantages—access control, IP hiding, geo-targeting—without configuring browser proxy settings, managing proxy servers, or maintaining IP pools.
Forward Proxy Authentication
Forward proxies implement authentication to prevent unauthorized usage and control access. Common authentication methods include username/password credentials sent through the Proxy-Authorization header, IP whitelisting restricting access to known client addresses, and API key authentication for programmatic access.
Corporate forward proxies often integrate with Active Directory or LDAP for centralized credential management, enabling single sign-on where employees authenticate once to the corporate network and gain automatic proxy access without separate credentials.
Best Practices for Forward Proxies
Configure appropriate access controls preventing unauthorized proxy usage. Open forward proxies without authentication become targets for abuse—spam operations, illegal content access, or attack laundering. Require strong authentication and regularly audit authorized users.
Implement comprehensive logging tracking all requests passing through the forward proxy. Log client identities, requested URLs, timestamps, and response codes for security auditing, policy compliance, and troubleshooting. Retain logs according to organizational policies and regulatory requirements.
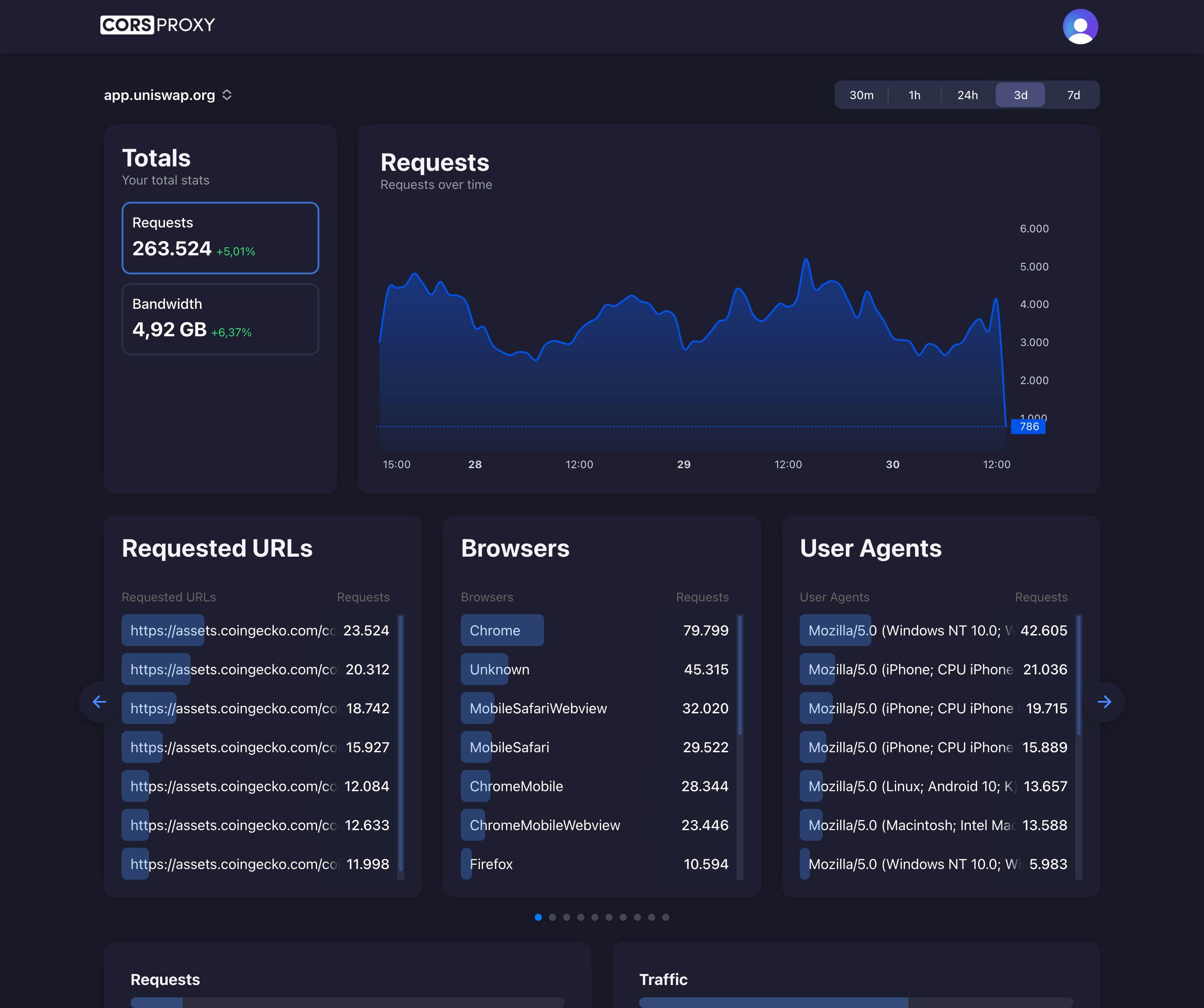
Monitor proxy performance and usage patterns detecting anomalies, capacity issues, and potential abuse. Track bandwidth consumption, request rates, error rates, and client activity. Unusual traffic spikes may indicate compromised credentials, automated abuse, or capacity problems requiring investigation.
Maintain proxy security through regular software updates, security patches, and configuration hardening. Disable unnecessary features, implement connection limits, configure appropriate timeouts preventing resource exhaustion, and restrict management access to authorized administrators only.
Advantages of Forward Proxies
Centralized access control simplifies internet access management across organizations. Single policy enforcement point controls what employees can access, implements time-based restrictions, scans for malware, and blocks malicious sites without configuring individual devices.
Enhanced privacy protects user identities and browsing habits. Forward proxies hide client IP addresses from destination servers, preventing IP-based tracking and profiling. Users maintain anonymity while browsing, protecting personal information from surveillance and data collection.
Performance optimization through content caching reduces bandwidth costs and improves response times. Frequently accessed content serves from proxy cache rather than repeatedly fetching from origin servers. Organizations save bandwidth costs while users experience faster page loads.
Limitations of Forward Proxies
Configuration requirements mean clients must explicitly configure forward proxy settings in applications or operating systems. Unlike transparent proxies that intercept traffic automatically, forward proxies need per-application or system-wide configuration. This setup barrier affects deployment ease and user experience.
Single point of failure creates vulnerability if the forward proxy fails. All client internet access depends on proxy availability. Proxy outages halt all internet connectivity for users routing through the proxy. High availability configurations with redundant proxies mitigate this risk.
Performance bottlenecks occur when forward proxies become overloaded or poorly configured. Inadequate proxy capacity, insufficient bandwidth, or suboptimal caching degrades performance for all users. Proper capacity planning and performance monitoring ensure proxy infrastructure scales with user demands.
When to Choose Forward Proxies
Choose forward proxies for organizational internet access control and policy enforcement. Corporate environments benefit from centralized management of employee internet usage, security scanning, and compliance logging that forward proxies provide.
Use forward proxies for privacy protection and anonymity needs. Individuals seeking to hide IP addresses, avoid tracking, or bypass geo-restrictions achieve these goals through forward proxy services offering residential or datacenter IPs in desired locations.
Skip forward proxies for server-side traffic management needs. Those use cases require reverse proxies providing load balancing, SSL termination, and backend protection. Forward proxies serve client needs while reverse proxies serve server infrastructure.